
"Our tailored course provided a well rounded introduction and also covered some intermediate level topics that we needed to know. Clive gave us some best practice ideas and tips to take away. Fast paced but the instructor never lost any of the delegates"
Brian Leek, Data Analyst, May 2022







Scala is a new and exciting programming language that is a hybrid between object oriented languages such as Java and functional languages such as Haskell. As such it has its own programming idioms and development styles.
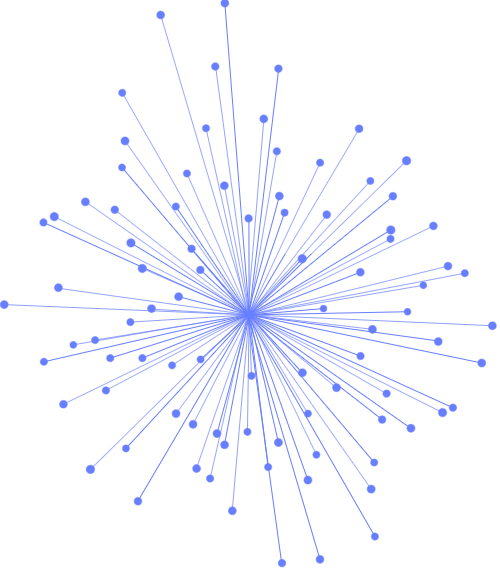
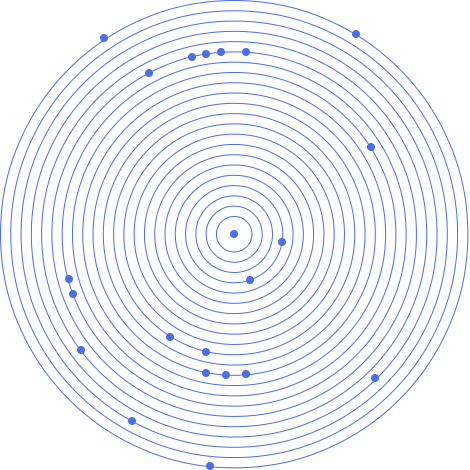
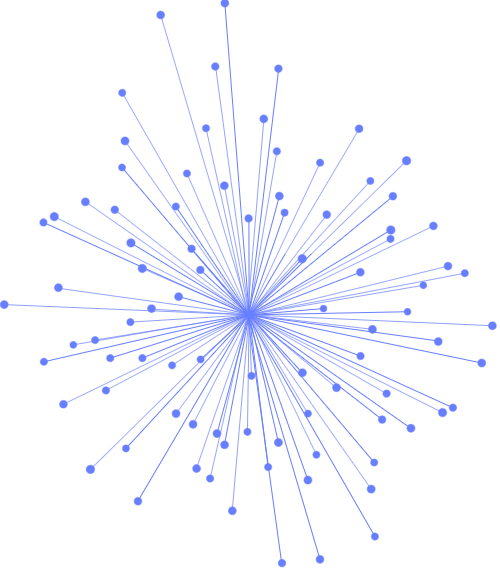
Scala Design Patterns looks at how code reuse can be successfully achieved in Scala. A major aspect of this is the reinterpretation of the original Gang of Four design patterns in terms of Scala and its language structures (that is the use of Traits, Classes, Objects and Functions). It includes an exploration of functional design patterns and considers how these can be interpreted in Scala's uniquely hybrid style.
A key aspect of the course is the many code examples that accompany each design pattern, allowing the reader to understand not just the design pattern but also to explore powerful and flexible Scala language features. Including numerous source code examples,
Part I – Introduction.- Introduction.- Design Patterns.- UML and Scala.-
Part II – Fundamental Patterns.- Immutability.- Singleton.- Marker Trait.- Delegation.-
Part III – Code Reuse Patterns.- Lazy Parameters.- Partially Applied Functions.- Trait Based Template Operation.- Stackable Traits.- Currying and Code Reuse.- Cake Pattern.- Structural Injection.- Implicit Injection Pattern.-
Part IV – Gang of Four Patterns.- Gang of Four Design Patterns.- Gang of Four Patterns Catalogs.- Factory Operation.- Abstract Factory Pattern.- Builder.- Adapter Pattern.- Decorator.- Facade.- Flyweight.- Proxy.- Filter.- Bridge.- Chain of Responsibility.- Command.- Strategy.- Mediator.- Observer.- State.- Visitor.- Memento.-
Part V – Functional Design Patterns.- Functor.- Applicative Functor.- Monoid Pattern.- Monad Pattern.- Foldable.- Zipper.- Lens Pattern.- View Pattern.- Arrow Pattern.

"Our tailored course provided a well rounded introduction and also covered some intermediate level topics that we needed to know. Clive gave us some best practice ideas and tips to take away. Fast paced but the instructor never lost any of the delegates"
Brian Leek, Data Analyst, May 2022
“JBI did a great job of customizing their syllabus to suit our business needs and also bringing our team up to speed on the current best practices. Our teams varied widely in terms of experience and the Instructor handled this particularly well - very impressive”
Brian F, Team Lead, RBS, Data Analysis Course, 20 April 2022
Sign up for the JBI Training newsletter to receive technology tips directly from our instructors - Analytics, AI, ML, DevOps, Web, Backend and Security.
Client feedback shows that delegates on our courses will best engage when they can relate course topics to their own day-to-day practices and requirements. Where possible, we run this course as a consultative, workshop-style event, in which discussion of relevant topics takes place in relation to the delegates' own applications and scenarios.
To facilitate this type of event, a subject matter expert leads the training, hands-on labs and discussions to ensure course topics are covered in a meaningful, relevant and timely manner. Delegates may be able to bring their own practical requirements and work to the course if the subjects and course topics are suitable.
CONTACT
+44 (0)20 8446 7555
Copyright © 2025 JBI Training. All Rights Reserved.
JB International Training Ltd - Company Registration Number: 08458005
Registered Address: Wohl Enterprise Hub, 2B Redbourne Avenue, London, N3 2BS
Modern Slavery Statement & Corporate Policies | Terms & Conditions | Contact Us
POPULAR
AI training courses CoPilot training course
Threat modelling training course Python for data analysts training course
Power BI training course Machine Learning training course
Spring Boot Microservices training course Terraform training course